 On multiple occasions we informed about a new threat to Polish online banking users, which we named VBKlip. This is a new kind of malware that substitutes the bank account number that has been copied to the clipboard. This works when we try to, e.g. pay a bill, and we copy the bank account number to paste it to the online banking wire transfer page. Instead of paying the bill we send that money to the attacker. In this article, we publish a detailed analysis of this threat. We consider it a serious threat, because we constantly receive reports from users that they have been infected with it and their money has been stolen.
On multiple occasions we informed about a new threat to Polish online banking users, which we named VBKlip. This is a new kind of malware that substitutes the bank account number that has been copied to the clipboard. This works when we try to, e.g. pay a bill, and we copy the bank account number to paste it to the online banking wire transfer page. Instead of paying the bill we send that money to the attacker. In this article, we publish a detailed analysis of this threat. We consider it a serious threat, because we constantly receive reports from users that they have been infected with it and their money has been stolen.
VBKlip.NET
After analyzing dozens of samples, we were able to divide VBKlip in two distinct families: one written in .NET and the second one written in Visual Basic 6. They are most probably created by two distinct individuals or groups.
Former malware family, written in .NET, was seen spreading by the existing botnets (e.g. Andromeda) and is run without the user interaction. Malware is very simple: it compares the content of the clipboard with two most popular account number formats in Poland. If this matches successfully VBKlip substitutes the account number with the one that is hardcoded in the application. There is no network traffic and no registry activity (aside from the usual one).
Malicious code defines one form (named
), which contains one
component, which in turn is responsible for invoking a function periodically. The form is not visible to the user, because one of its dimensions is set to 0 and the taskbar icon is disabled. After we blogged about this threat, antivirus solutions began to recognize this threat based on the new signatures.
However, the author of the malware began his counterattack. It was as simple as adding new buttons or labels to the invisible form. This usually resulted in a significant drop in the detection rate, from dozens of detections to just 5 or even less. There was also an additional code added, one which came from the Visual Basic tutorials and is presented below.
Sub givemessage()
MessageBox.Show("I am cool for using subs")
End Sub
Private Sub Button1_Click(ByVal sender As System.Object,
ByVal e As System.EventArgs)
Handles Button1.Click
Call givemessage()
End Sub
End Class
We were able to determine that the author most probably uses operating system from the Windows family, Vista or newer, and his account is
. This machine is also most probably a virtual machine. Author is comfortable with using Polish language and names the binaries using that language. He also made sure that malware pretended to be an update of the popular applications like Adobe Flash Player, Facebook Chat or Java.
VBKlip in Visual Basic 6
The Visual Basic version did not have significant upgrades, since we last blogged about it. It was also written by a person who is comfortable with the Polish language. Recently it has began using the C&C server to get the new account numbers. It also sends e-mail (using SMTP) to the author containing information about the account number substitutions. We were unable to find any connections with the .NET version.
This malware was distributed using a spear phishing technique with two kinds of e-mails. First kind was an e-mail targeting Allegro (Polish online auction website) merchants. Message content was written as a letter of complaint and suggested that the attachment contained photos of the disputed item. Attachment was either a zip file containing the Windows Screesaver file or just an
file. The basename of the file ended with
and had a JPEG icon. The letter of complaint was in line with the goods that merchant offered on the auction website. Second type of messages was send to the accounting departments of companies, suggesting that the attached file is an invoice. File basename ended with
and the icon suggested it was a PDF file. Filenames were also personalized to point to the recipient.
This malware unpacked a zip archive to the user’s temporary directory (
). If this was a version that pretended to be an invoice it also tried to open an empty PDF files with a default PDF reader. Adobe Reader reports this file as “broken”, which is enough to convince the user that the invoice is corrupted.
Next, in order to get the new account number for the switch, VBKlip contacted the C&C server. This server answered with encoded account number. In case of connection problems or when server simply did not respond, VBKlip used an account number from configuration. Server was configured to only answer to requests with a specific
header. This was made in order to be sure that it was the malware that sent the request, and not a normal browser.
SMTP provides an additional channel for communication. Message send from an address in the
domain, contains information specific to the computer which the sample was run on. In some cases whole list of active processes is provided. Bot also sends a periodic reports about its activities. This contains an information about the website from which the account number was copied or to which it was pasted, along with the bank ID. This ID is based on the website title, as displayed in the browser window. Malware searches for the following strings:
- Alior
- eBG
- E-BG
- Bank Ochrony
- Agricole
- WBK S
- eurobank
- GETIN Bank
- ING Bank
- nteligo [sic!]
- INVEST-BANK
- iPKO
- mBank
- MultiBank
- Pekao24
- Pocztowy
- Raiffeisen
- bank numerical ID, marked as
<span class="text">nrB</span>
,
- browser name, marked as
<span class="text">Br</span>
,
- computer name (as a name of mail sender),
- user name (as a name of the e-mail recipient),
- local time and malware version (as an e-mail subject),
- URL and browser window title (both when copying and pasting marked as
<span class="text">URL</span>
and
<span class="text">Sub</span>, respectively),
- selected numbers from the money mule account number (marked as
<span class="text">Ref1</span>
).
If the website title did not match any of the strings, it was saved as unknown (with
ID). Additionally,
and
were sharing a common ID.
Malware consists of several different components, which share names with a common Windows processes. Every one of the components has different functionality. The execution tree of one of the samples is pictured below, with
being a legitimate Windows process.
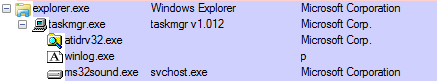
Due to this separation of functions, even if antivirus solutions detect one of the components, all other remain working. Best example of this case is when an antivirus solution detect the component responsible for the network communication and terminates it. However, it leaves the component responsible for the clipboard substitution, which means that the core functionality of the malware is not hindered.
 atidrv32.exe
atidrv32.exe
atidrv32.exe
First of the described components is responsible for logging. It also is the one that translates bank names to IDs and tracks the copy & paste operations. All this reports are saved to the
text file. This informations includes, among other things:
 winlog.exe
winlog.exe
This component is responsible for the account number substitution. It also prevents the user from pasting the money mule account to the windows that have title containing
,
or
in it (”notatnik” means “notepad” in Polish). This prevents user from using the easiest detection method – copying and pasting the test account number to Notepad, MS Word or WordPad to see if it has changed. Communication is encrypted using a simple substitution cipher – one of the set of four ASCII letters correspond to one digit. Component also logs all of the clipboard uses and saves them along with the active windows title.
 taskmgr.exe
taskmgr.exe
This component is responsible for the network communication and creating a process tree. It is a common target for the antivirus solutions. As we stated previously, termination of this component does not mean that the malware is not working. Clipboard content still will be substituted by
. This component is also responsible for the process tree maintenance. If user (or the anvirius) terminates one of the other components,
restarts that component. Component naming scheme utilizes a simple social engineering – user is reluctant to terminate
process from the Task Manager window, because she will think that it is the Task Manager itself. However, this malicious process is easily recognizable: it is a 32-bit process with a unusual description:
.
 ms32sound.exe
ms32sound.exe
ast of the described components is responsible for the keylogging. This logs are saved to the
text file using a simple encoding. This is also based on a previously mentioned substitution cipher, which translates one digit (0-9) to one of the four ASCII letters corresponding to that number. This makes it easy to encode the account bank numbers, but makes it more difficult to encode an arbitrary character. In order to encode ASCII character it is first translated to thee digit number in decimal system (e.g.
->
). Then, digits are cyclically shifted to right (e.g.
->
). Then each of the digits is translated using a mentioned dictionary.
VBKlip – are these new actors, or just new techniques?
This month we have observed new samples of VBKlip. The .NET version have been obfuscated in order to make the analysis more difficult. It also pretends to be MS Word and open notepad when executed. This may suggest that the author changed the distribution strategy from botnet to e.g. phishing and was able to afford a .NET packer or learned to use one. We also cannot rule out that this was created by yet another attacker, not connected with the two mentioned in the post.
VBKlip written in Visual Basic 6 started to use a different C&C server. This is not the only important change (as this, on itself, would not be anything worth noting) the component names have changed and the C&C was misconfigured. It did not accept (invalid) HTTP header
, which made the malware non usable. However, e-mail accounts were still in the
domain.
This may suggest that the malware was sold to some third party, or author tries (unsuccessfully) to rebuild his botnet.
Summary
VBKlip remains a real threat, despite collective efforts to raise people awareness. Of course, it has a smaller impact than at the beginning of the malware campaign. We are still receiving reports from users affected by this malware and we advice everyone to double check the account number, when they are performing a wire transfer. If you are using one time passwords based on text messages, it is best to compare the recipient’s account number with the account number in the text message. Of course, there still is a possibility that someone used clipboard to copy account number to the invoice that you have received.
